New Delhi: Microsoft researchers have flagged a malware campaign that spreads through WhatsApp, and honestly, it feels a bit too easy. No complex trick. Just a file, a click, and things start going wrong quietly.
The activity showed up in late February 2026, based on findings from Microsoft Defender Security Research. It uses VBS files. Most people won’t even recognise the format. You open it thinking it’s nothing, and that’s where it begins.
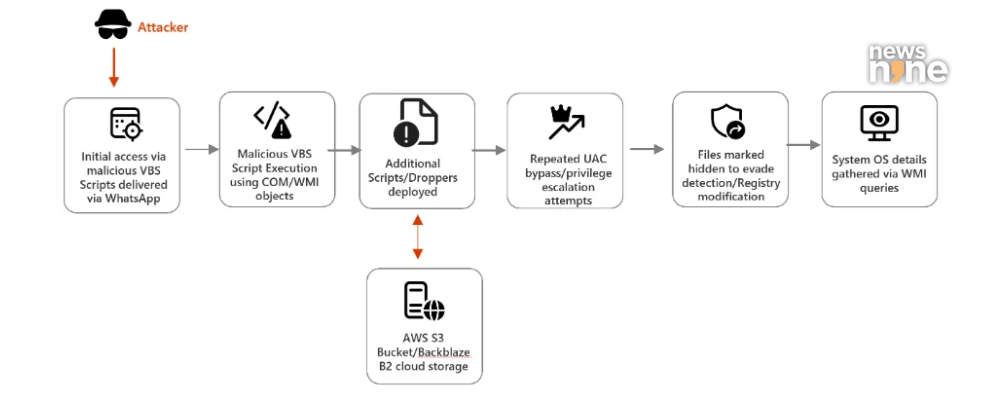
Infection chain – Source Microsoft
WhatsApp messages used as entry point
It starts with a message. Could be from someone you know. Could look harmless. That’s the catch.
Open the file, and the system begins to change in the background. Hidden folders appear. Real Windows tools get copied and renamed. curl.exe becomes something else. bitsadmin.exe too.
Microsoft said, “The campaign relies on a combination of social engineering and living-off-the-land techniques.”
Which is a fancy way of saying attackers are using your own system against you.
Malware uses trusted cloud platforms
Then it pulls more files from places you would normally trust.
| Platform | Role in attack |
|---|---|
| AWS S3 | Hosts payload files |
| Tencent Cloud | Delivers more scripts |
| Backblaze B2 | Stores extra components |
This is where it gets messy. The traffic looks normal. No obvious red flags. That makes it harder to catch.
Escalation and persistence mechanisms
Once inside, the malware tries to get admin control. It keeps pushing until it succeeds.
Microsoft noted, “Once the secondary payloads are in place, the malware begins tampering with User Account Control (UAC) settings to weaken system defenses.”
After that, attackers install MSI packages. Some include remote tools like AnyDesk. And at that point, the system is not really yours anymore.
Microsoft added attackers “use renamed Windows utilities to blend into normal system activity.”
So everything looks fine, until it isn’t.
User caution remains critical
This still comes down to one small action. Opening a file you didn’t expect.
Even if it’s from a contact, it’s worth pausing for a second. That one second might save a lot of trouble.
