New Delhi: A popular AI developer tool is now at the centre of a serious supply chain attack, and this one feels close to home for many developers. LiteLLM, a package with around 97 million downloads, was reportedly compromised on PyPI with a malicious update that quietly slipped into systems.
The original report by Callum McMahon flagged the issue early, and the community quickly jumped in to contain the damage.
What went wrong with LiteLLM
The issue started when version 1.82.8 of LiteLLM was uploaded to PyPI. There was no matching GitHub release that itself raised a red flag.
Inside the package, a hidden file triggered automatically every time Python started. This file launched repeated processes, creating what the report described as an exponential fork bomb that crashed systems.
The malware worked in stages. It collected sensitive data like SSH keys, cloud credentials, and environment files. Then it encrypted and sent that data to an external server. It even tried to move across Kubernetes clusters and install backdoors.
How the attack unfolded on a real machine
McMahon shared a personal account that makes this more real. He noticed his system was slowing down badly. CPU usage hit 100 per cent. Thousands of processes were running.
He said, “my machine stuttering hard, something that really shouldn’t be happening on a 48GB Mac.”
The root cause turned out to be an unpinned dependency. A tool automatically pulled the latest LiteLLM version, which had already been compromised.
The malware behaviour
| Stage | What it did |
|---|---|
| Collection | Pulled SSH keys, cloud tokens, passwords, configs |
| Exfiltration | Encrypted data and sent it to a fake domain |
| Spread | Tried to access Kubernetes and create backdoors |
Who is behind the LiteLLM attack?
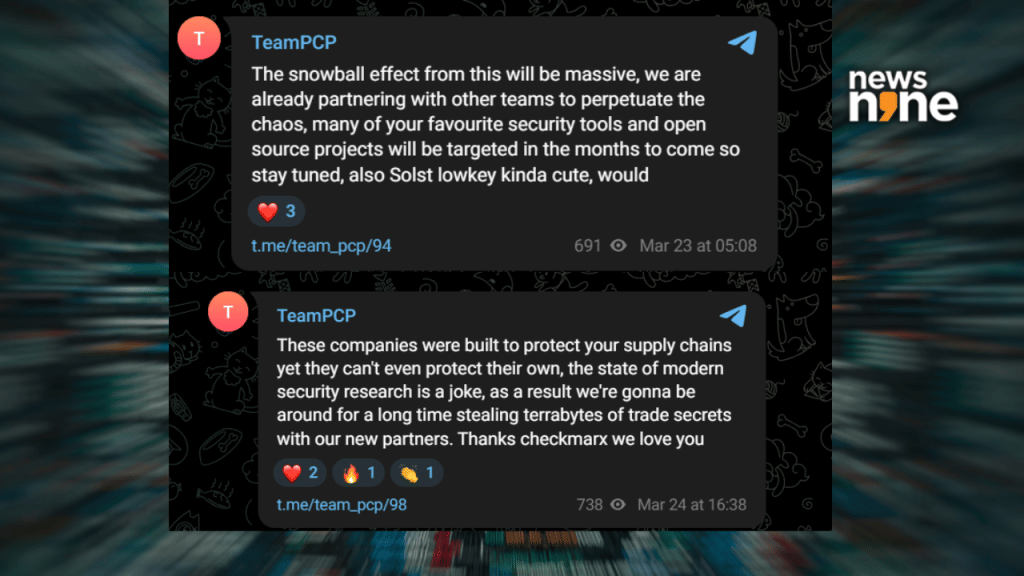
A threat group known as TeamPCP is said to be behind the LiteLLM attack. TeamPCP has been reported to be behind earlier attacks on Trivy and KICS as well. Multiple security firms have linked TeamPCP to be running a coordinated campaign targeting open source tools and developer infrastructure. The group has now started taking public credit for multiple attacks across ecosystems, pointing to a long-term operation focused on high-impact supply chain entry points.
The attackers themselves signalled more trouble ahead. In a Telegram post, TeamPCP mocked the security industry, claiming that tools built to protect supply chains are failing at their own security. The group said it plans to continue stealing large volumes of data and hinted at partnerships with other threat actors to expand its reach.
LiteLLM Compromise Linked to Wider TeamPCP Cyber Campaign
What developers should do now
The compromised versions have now been removed from PyPI, but the risk remains for those who installed them.
If you are one of the unlucky ones, you could start by checking installed versions, clearing caches, removing suspicious files, and rotating all credentials. The report by McMahon warns that any exposed system should be treated as compromised.